Recommendation algorithms and automated checks of classified documents as well as anomaly detection using Deep Learning at critical network transitions can increase information assurance and trustworthiness when dealing with sensitive data
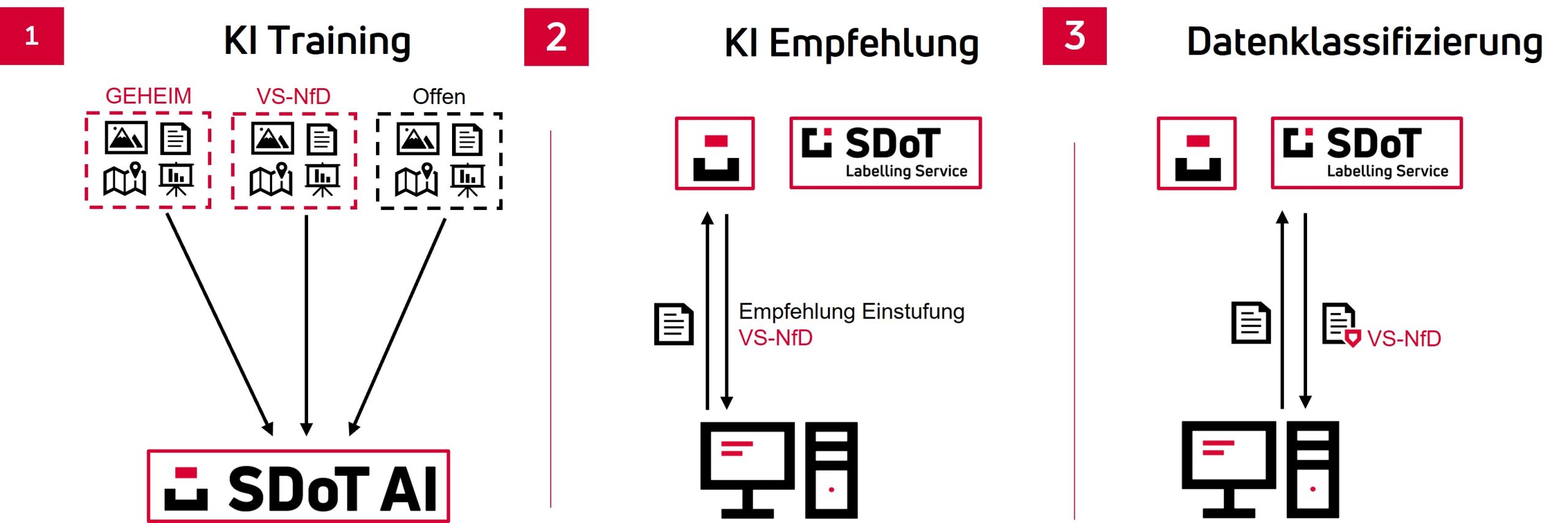
Artificial intelligence (AI) is a current trending topic in digitization. The development has been rapid so far and sure enough, AI is yet to develop its full impact in its entirety. Today, AI-based methods and systems can already lead to significant efficiency and security benefits – even in the high-security sector. Here, for example, an AI model can be trained with a small amount of classified data (Figure 1). This enables the AI to provide suggestions for classification (e.g., Restricted and the associated digital security labels for comparable data (e.g., PDF documents) so that the data can be shared through network transitions (Cross Domain Solutions) (Figure 2).
Figure 1: Support for data classification by SDoT AI Data Classifier (source: infodas).
The factors that need to be considered to classify data increase in number and complexity as digitization increases, and so do the uncertainties of non-routine users. AI-based systems can easily remedy this with classification recommendations – these know more data than any human user and can be integrated into any “registry” tool or other applications (e.g. Outlook) without changes to existing work processes. The principle is similar to product recommendations from online stores or systems for image-based diagnoses (CT, MRI or X-ray images) in the medical field. In the end, however, the user would and must decide.
The creation of the security label for a data object is done by the SDoT Labelling Service. The XML security label is cryptographically bound to a data object according to NATO standards and can contain further information (e.g. the creator or recipient group) in addition to the classification. The smallest changes to a data object automatically cause a security label to lose its validity and thus be blocked during data exchange.
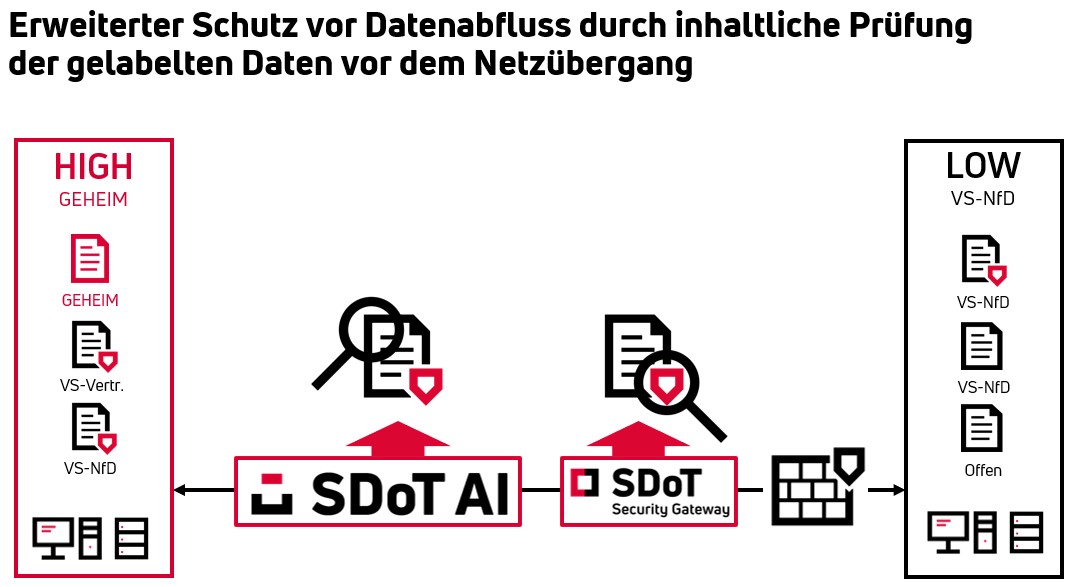
A further security gain could be achieved in cases of internal perpetrators or human errors of judgment through the use of AI (Figure 2).
Figure 2: Enhanced protection against data leakage by checking the content of the labeled data with AI before the network transition (source: infodas).
The bi-directional SDoT Security Gateway always checks or prevents the entire data exchange as a network transition between two different security domains. This is done on the basis of rule sets and security labels. When security labels are used, the content of the data object (e.g. DOCX) is not yet checked to determine whether it has been correctly classified.
Security labels can only be created by authorized personnel. However, this personnel can consciously (internal perpetrators) or unconsciously select a classification that is too low for a data object that is regularly classified higher. This can lead to unintentional data outflows from a security domain despite network transitions.
There is potential for optimization here using AI-based methods: Before the data object and the associated security label are checked in the SDoT Security Gateway, a content analysis including a classification proposal is performed by the AI. If this proposal matches the classification of the security label, the data object can be transmitted. In the event of a discrepancy, the transfer is stopped and an additional verification routine is performed using the 4-eyes principle.
AI would also be helpful in other respects: in addition to the security labels of the data according to VS instructions, it would also be conceivable that the implementation of data protection according to DSGVO would be supported without having to manually check all documents.