Key Features
L4Re Microkernel OS
All SDoT products use L4Re, a proprietary microkernel operating system with proven security and separation mechanisms. Vulnerabilities like buffer overflows, memory leaks or deadlocks are avoided. Compared to standard operating systems such as Linux or Windows with a 15 to 50 million lines of code, L4Re OS has only 15,000 lines of code. L4Re Os is based on the L4 microkernel (µ-kernel) family, which goes back to the work of German computer scientist Jochen Liedtke. Other variations of L4 are used in Apple processors, Qualcomm chips or for autonomous systems (e.g. drones).
Overview of SDoT products
Bi-directional data exchange and filtering of structured and unstructured data objects.
Comprehensive cybersecurity for the industrial sector that ensures fully secured and controlled data exchange between different security domains (OT/IT).
For scenarios that require high-speed, low latency data filtering of structured data objects.
The fastest software-based Data Diode in the World with a German, EU and NATO SECRET accreditation
Application independent data classification with tamper proof and NATO STANAG 4774/8 compliant XML security labels.
SDoT Classified Information Registry – Manage digital and physical classified information
SDoT COMPACT-LAND – Unidirectional or bi-directional data transfer in vehicles and any climate zone
Cross Domain Solution Scenarios
The Secure Domain Transition (SDoT) product family allows controlled unidirectional or bi-directional exchange of data between networks/systems of different sensitivity level as well as the creation of NATO STANAG 4774/8 compliant and tamper proof security labels. The SDoT product family offers the most comprehensive cross domain solutions on the market for network security and data leakage prevention (DLP). SDoT products enable digitization in sensitive or highly critical areas, as data is exchanged and made available in a controlled manner while sensitive data remains protected.
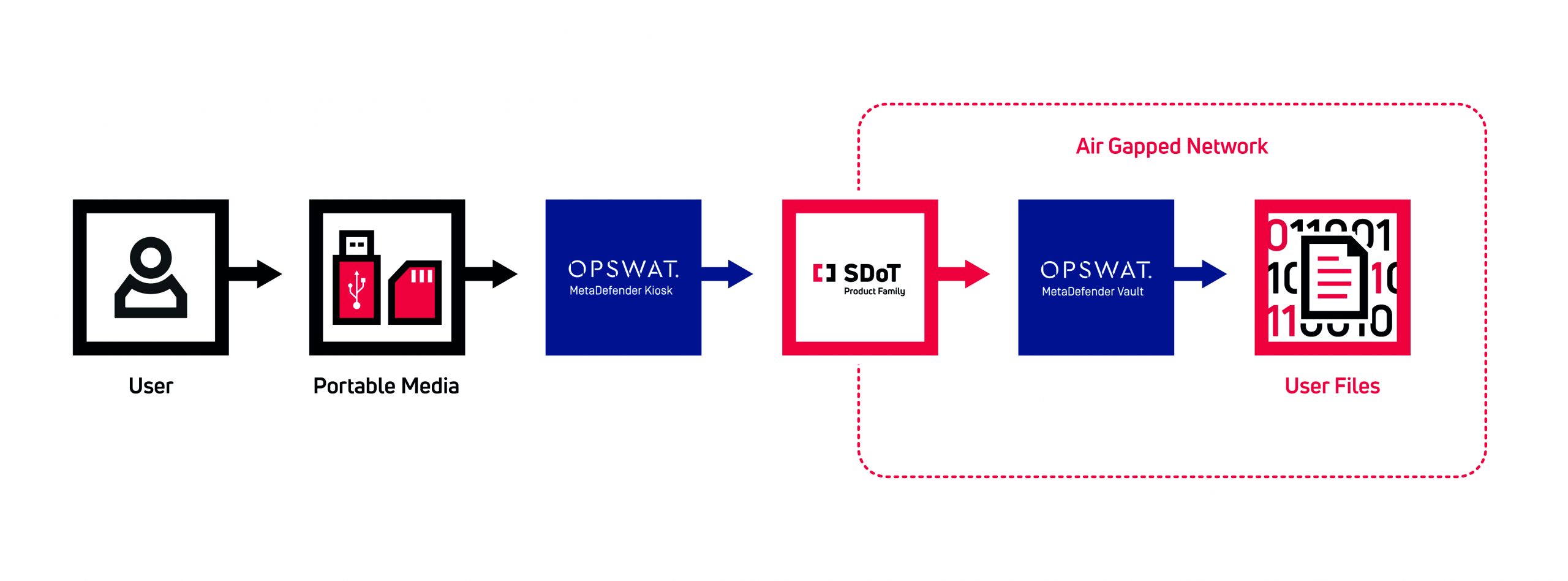
Combining the SDoT products with the OPSWAT MetaDefender Kiosk and MetaDefender Vault protects sensitive networks from malware. Risks are not only detected, but also subjected to a secure and controlled scanning and cleaning process using over 35 anti-malware engines.
What are Cross Domain Solutions?
Test Now
Request a Proposal
Discuss use-case